Let's talk: +49 (0) 228 50431650 | Mail: info@e2security.de
HTTP Verb Tampering
For English, please scroll to the end of this blog article
Für Englisch, scrollen Sie bitte an das Ende dieses Blogartikels
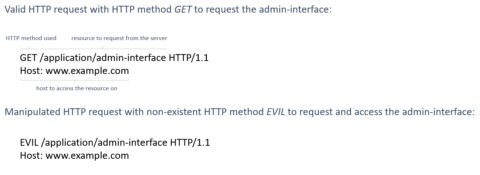
When testing web applications for security flaws, the applications’ handling of different HTTP request methods – also known as verbs – should be considered.Usually, interactions between clients and servers utilize the HTTP methods GET or POST for accessing resources.
How would an application react if it receives HTTP requests from a client with unexpected or unimplemented HTTP methods, for example? In some cases, tampering the HTTP method might lead to a bypass of authentication and access control mechanisms: imagine a web application that enforces an HTTP basic authentication on a resource when receiving a HTTP request for it with the HTTP method GET – this resource can be for example an admin interface. Now, if the HTTP method is manipulated, it may happen that the authentication is successfully bypassed, and an attacker is granted access to that admin interface.
What is the risk?
As described earlier, testing for HTTP verb tampering might lead to the discovery of flaws in authentication and access control mechanisms. Such vulnerabilities can signify loss of confidentiality and integrity, potentially meaning high-risk impacts on businesses.
How to remediate?
Primarily, a web application might be vulnerable for HTTP verb tampering attacks if one of the following conditions are met:
- the web application uses a security control that lists HTTP verbs
- the security control fails to block verbs that are not listed
- a GET verb is used that is not idempotent or will execute with an arbitrary HTTP verb
When it comes to remediation, the applications’ source code should be checked whether any of the above conditions are met. Please be aware that different web servers, frameworks and programming languages handle the implementation of these vulnerable conditions differently.
Real life examples
Although searching for http verb tampering in popular vulnerability records yields only a handful of results (Search in CVE database: https://cve.mitre.org/cgi-bin/cvekey.cgi?keyword=HTTP+verb+tampering), these vulnerabilities still exist in modern web applications. For example:
- CVE-2020-4779 is assigned to a recent issue in a product of IBM. (https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-4779)
- CVE-2018-2483 belongs to a product of SAP. (https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-2483)
Der Beitrag HTTP Verb Tampering erschien zuerst auf e2 Security.

Let's talk.
You have questions about this article or want a consultation?
Please contact us directly!

e2 Security
Wir treiben die digitale Transformation voran, indem wir Cybersicherheit direkt in die Wertschöpfungskette Ihres Unternehmens integrieren.